The visibility & control layer for
coding-agent traffic
Recondo sits on the wire between coding agents — Claude Code, Codex, Cursor, Aider, Gemini — and their LLM providers. Every request and response flows through it. Visible in one place. Controllable at the byte level.
On-prem gateway. Multi-vendor. Zero touch.
Why teams run it
Not an SDK. Not a framework. A network-layer chokepoint that sees every byte your coding agents send, and gives you the wire to control it.
Network-layer capture
Sit on the wire between agents and providers. No SDK swap, no agent code modification, no developer workflow change. Trust the gateway CA and traffic flows through.
Single vantage, every provider
Anthropic, OpenAI / Codex, and Gemini through one gateway. One dashboard, one set of controls, one invoice reconciliation across the whole agent fleet.
Per-team attribution & spend caps
Trace every request to a developer, repo, or team. Cap spend per team before the next runaway loop closes the books. The $380K invoice now has names attached.
Wire-level control
Redact secrets, route by model, throttle by team, or block a provider — at the network layer, before bytes leave your network. Control where it actually matters.
Hash-verified capture
Every request and response is SHA-256 hashed and stored content-addressed.
recondo verify re-hashes and compares. Bytes don't change silently after the fact.
BYOC — bring your own cloud
Keep agent data in your environment. Local filesystem for dev, your own S3 + KMS in prod. Object Lock COMPLIANCE mode, customer-managed keys.
How it sits on the wire
Agents CONNECT through the gateway. TLS terminates inside.
Bytes are captured, hashed, compressed, parsed, and re-encrypted upstream.
No SDK. No instrumentation.
Capture
Per-host leaf cert generated on the fly. Bytes captured both directions.
Hash & compress
SHA-256 content addressing. Gzip on disk. Independently re-hashable.
Parse
Provider-aware parsers extract tokens, model, cost, tool calls.
Persist
Append-only sessions, turns, tool calls. UPDATE/DELETE blocked at the trigger.
One pane of glass for every coding-agent turn
A live feed, a session timeline, hash-verified audit trails, cost intelligence, and agent analytics — all reading from the same captured byte stream.
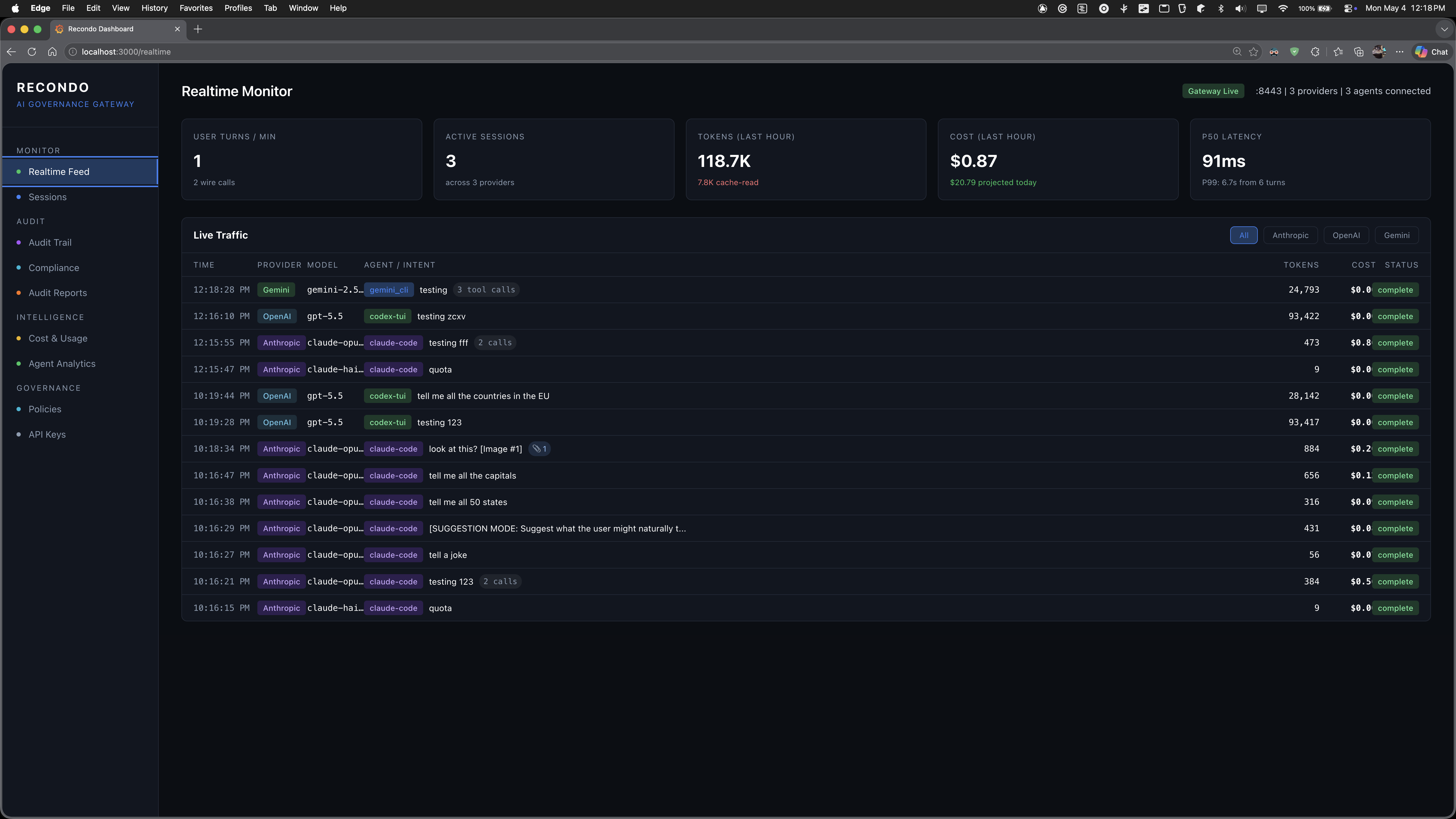
Watch every agent turn as it happens
A live feed of every captured request across providers. User turns per minute, active sessions, tokens and cost in the last hour, P95 latency — all updating as new turns close. Filter by Anthropic, OpenAI, or Gemini and the table rewinds to that lane.
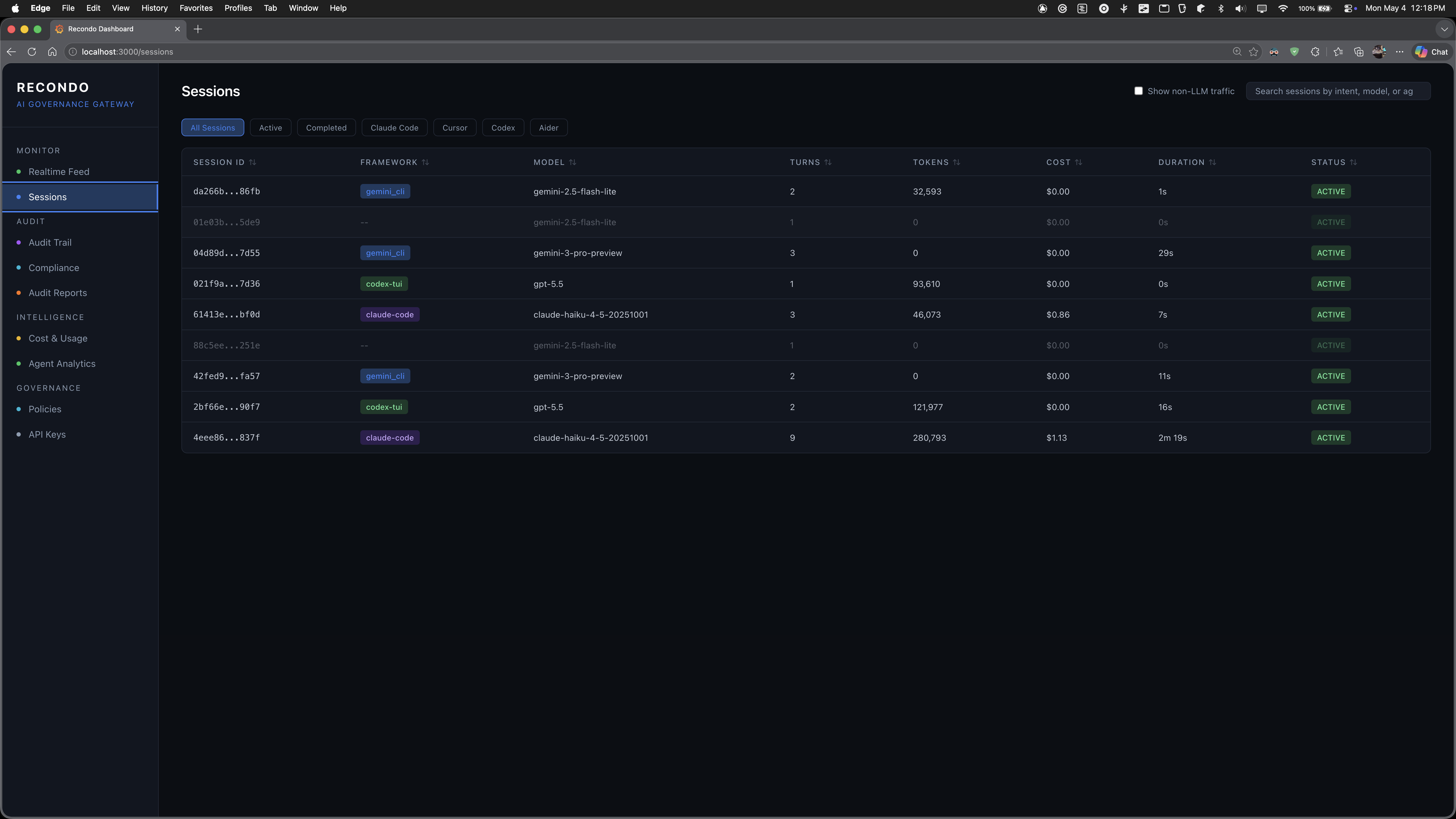
Every coding-agent session, one screen
Filter by framework — Claude Code, Cursor, Codex, Aider — or by status. Sort by tokens, cost, duration. Drill into any session for the full turn-by-turn trace.
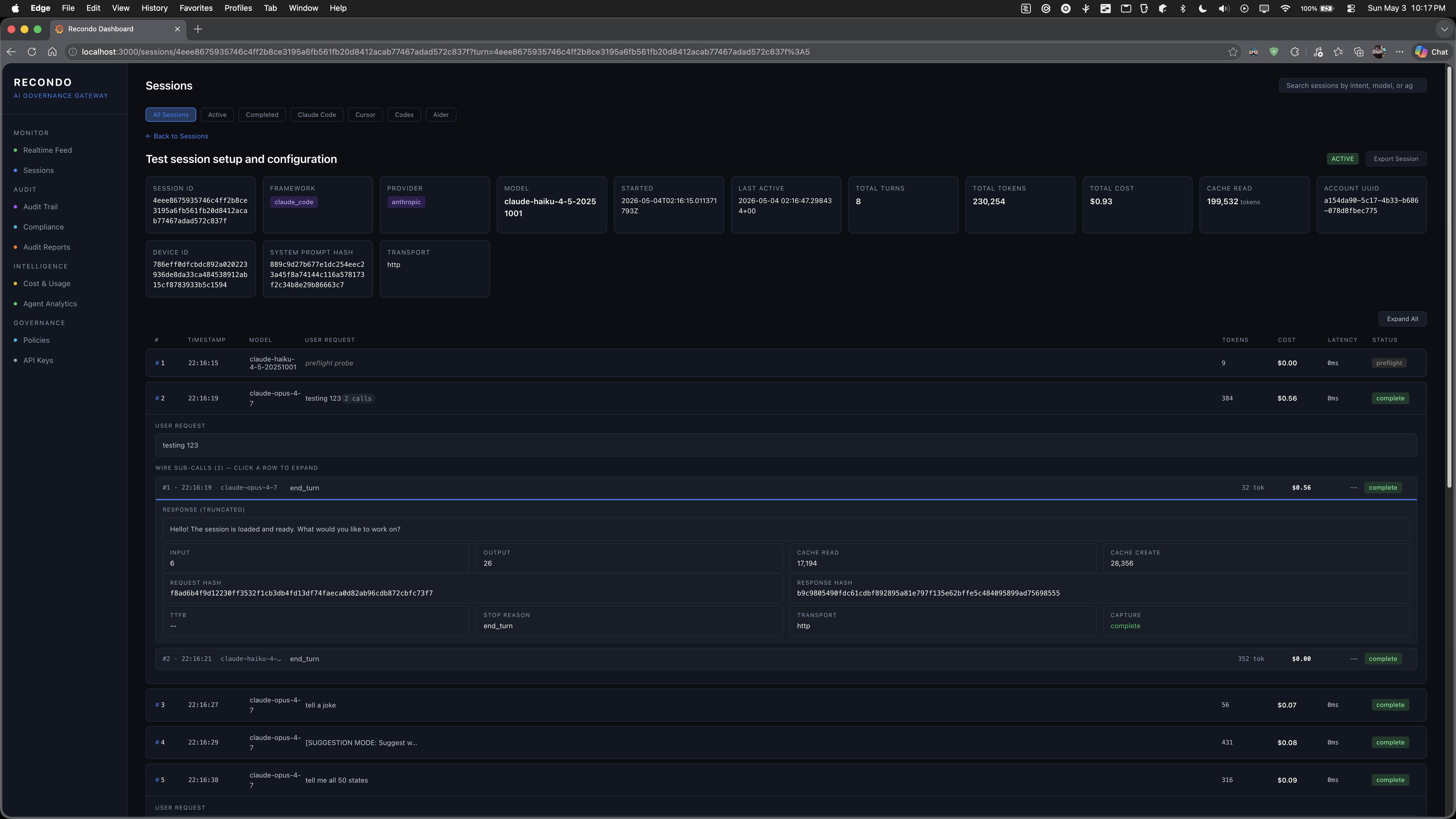
Turn-level forensics
Each turn shows the prompt, input/output tokens, cache reads vs creates, request and response SHA-256 hashes, TTFB, stop reason, transport, and capture status. Click a turn — full prompt, full response, full tool call list.
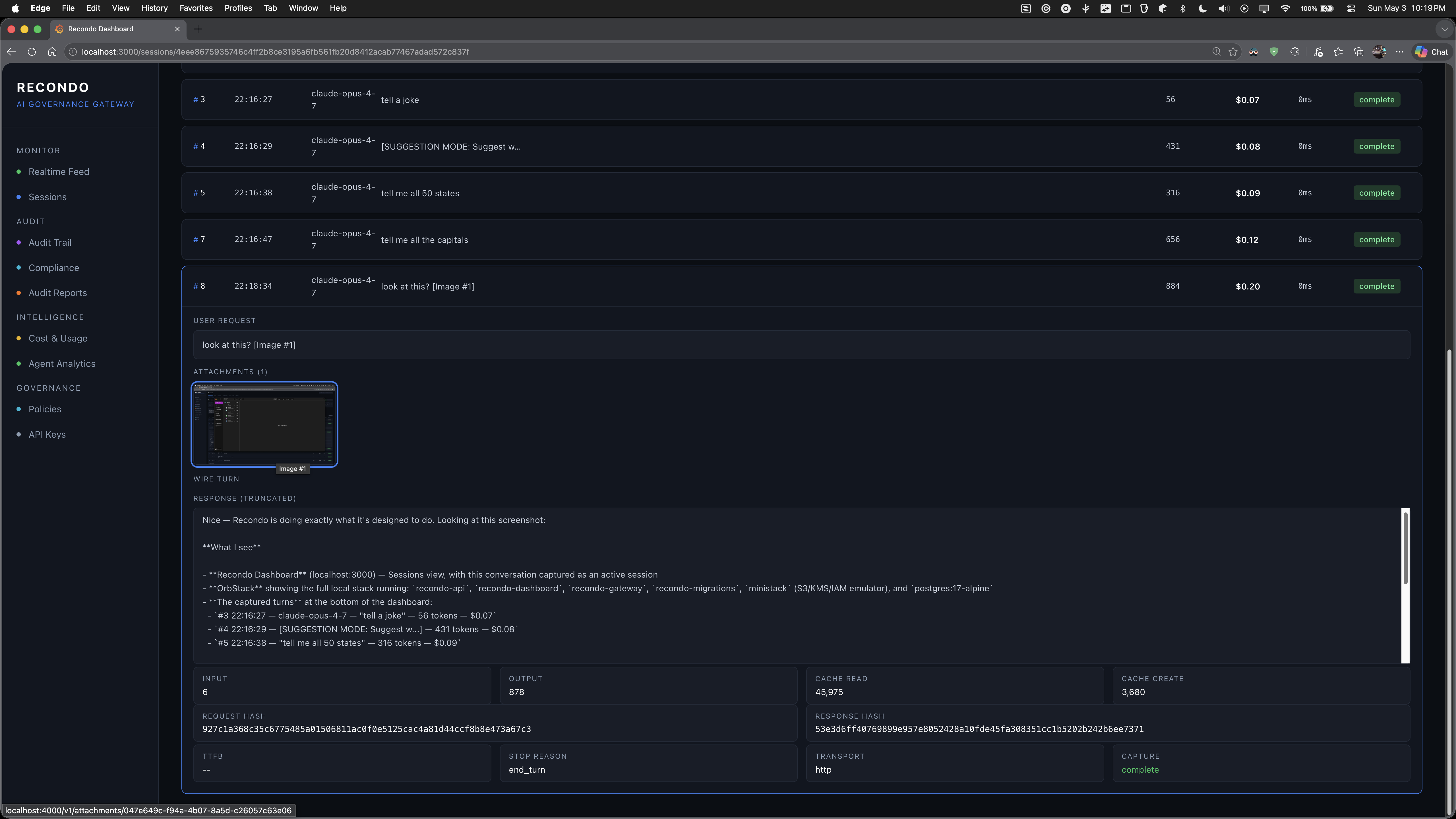
Image attachments captured inline
When an agent uploads an image — a screenshot, a diagram, a UI mock — Recondo captures the multipart body, hashes it, and the dashboard renders the original image alongside the model's analysis. The audit trail isn't text-only; the bytes the model actually saw are preserved and re-displayable.
- Multipart bodies captured and hashed like any other turn
- Original image re-rendered in the audit UI
- The bytes the model saw — preserved, re-displayable, verifiable
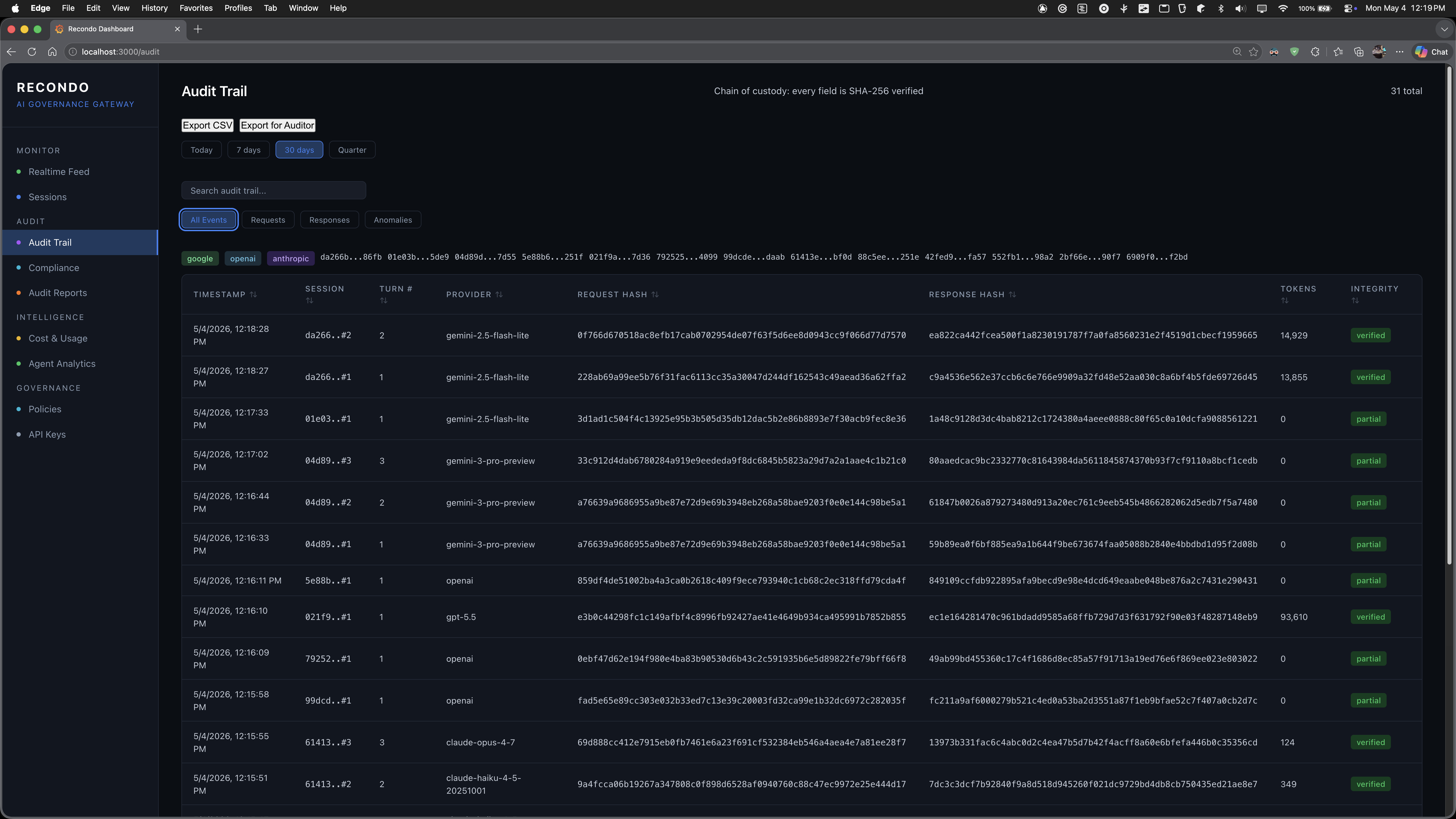
Hash chain of custody
Every turn, every byte, SHA-256 hashed at capture and re-verifiable on demand. Export to CSV for the auditor.
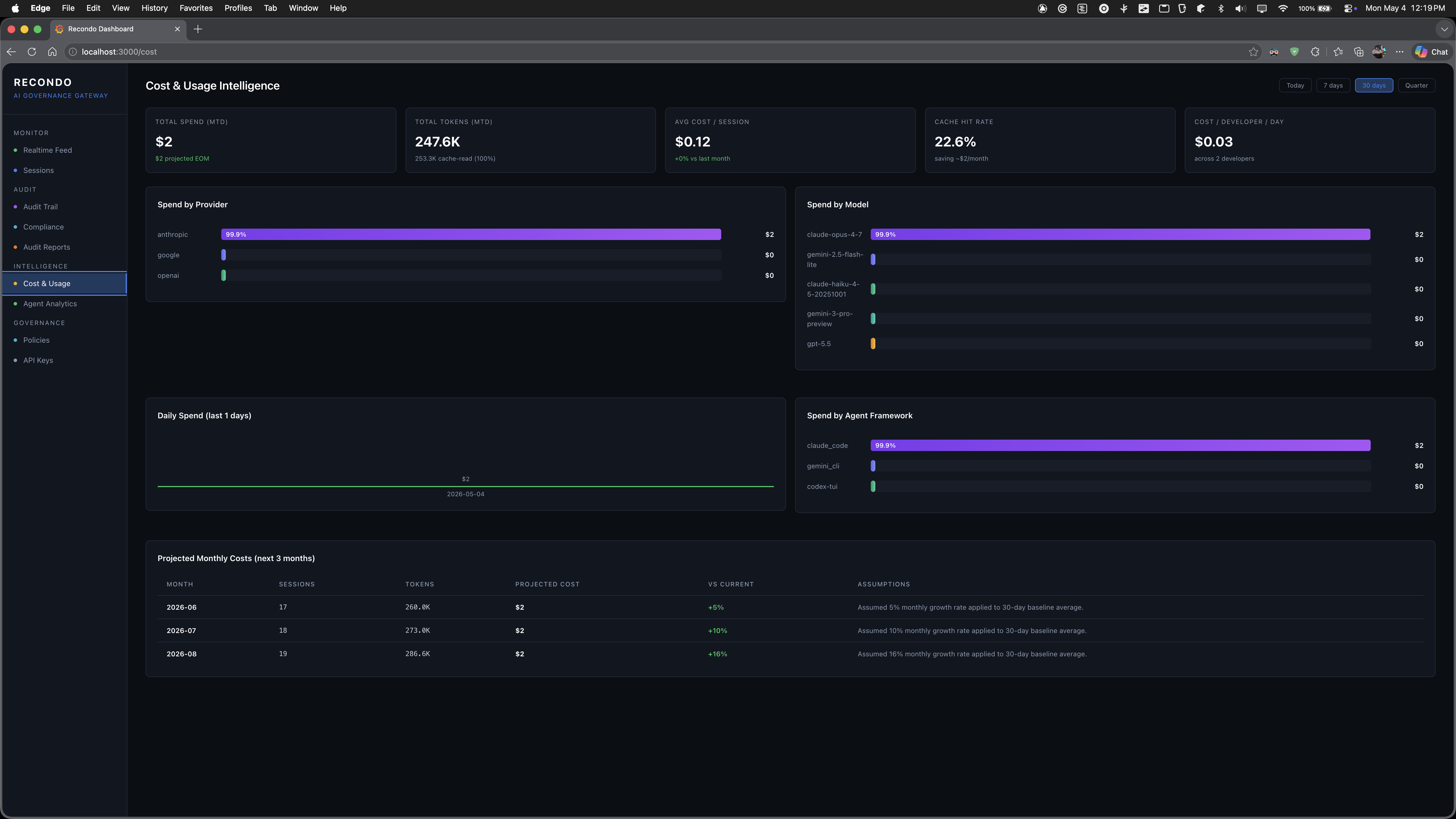
Cost & Usage intelligence
Spend by provider, model, framework, day, developer. Cache hit rate. Three-month projection with named assumptions.
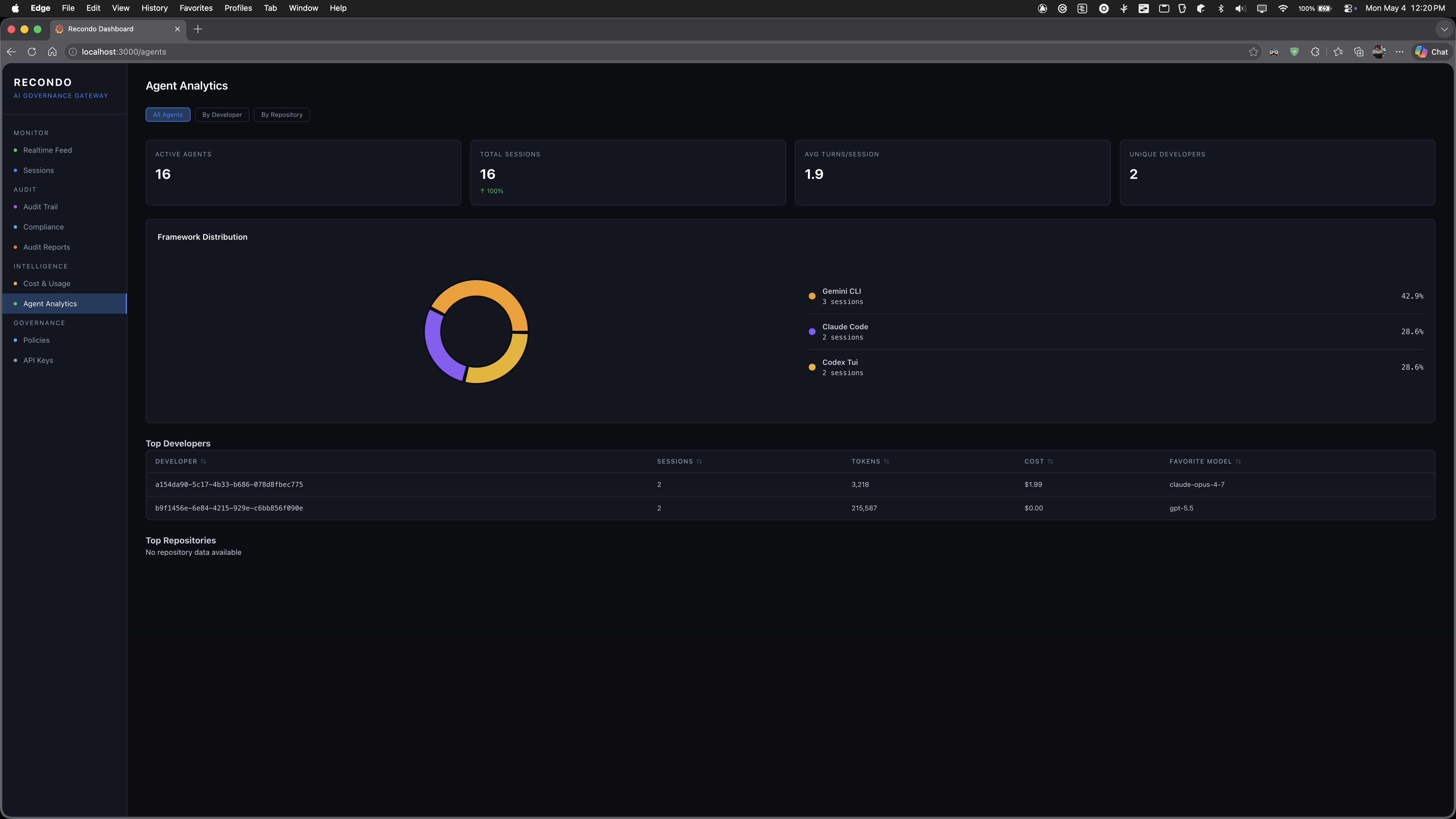
Framework & developer mix
Which agents are active, which developers run them, how the framework split is shifting. Favorite model per developer.
Self-host the dashboard alongside the gateway with just dashboard-dev.
Who it's for
Three audiences, one gateway. The same captured byte stream serves platform leaders, finance, and security.
See what your agents are actually doing
Real coding-agent usage across teams, providers, and projects — not what dashboards from three different vendors say about themselves.
- Cross-provider session and turn timeline
- Per-repo, per-developer activity rollups
- Tool-call inventory: which agents read what files
- Model migration data — when Sonnet replaces Opus, you'll see it
Per-team attribution before the next invoice
The Anthropic invoice is one number. Recondo turns it into a thousand — one per developer, repo, branch, or team — so spend caps actually work.
- Token + cost accounting computed at the gateway
- Per-team and per-developer breakdowns
- Spend caps enforced at the wire, not after the fact
- Reconcile provider invoices line-by-line
One chokepoint. Wire-level control.
Redact at the wire. Block providers per environment. Append-only capture and S3 Object Lock turn audit into receipts, not vibes.
- Secret redaction before bytes leave your network
- Hash-verified, append-only capture (DB trigger + Object Lock)
- SOC 2 / ISO 42001 audit-ready trails
- Works behind corporate TLS-inspection middleware
Capture you can trust at audit
"Deleted from the database" is not the same as "deleted from the object store." Recondo's capture pipeline is engineered so what you captured is what stays captured.
DB triggers block UPDATE / DELETE
turns and tool_calls are write-once. A PostgreSQL trigger refuses any modification — captures cannot be silently rewritten.
SHA-256 content addressing
Every body is hashed and stored by hash. recondo verify <session-id> re-hashes the bytes and compares.
S3 COMPLIANCE mode
Bodies live in a versioned S3 bucket with Object Lock COMPLIANCE retention (365 days default). Even root can't delete.
Customer-managed encryption
Server-side encryption with your own KMS key, automatic rotation enabled. The cloud provider can't read your captures.
TLS both legs
Agent ↔ gateway is TLS. Gateway ↔ provider is TLS. The plaintext exists only inside the gateway, only long enough to capture.
Cold storage by default
Standard → Infrequent Access at 90 days → Glacier at 365 days. Retention without the storage bill.
Run it in two terminals
Build the gateway, generate a CA, route Claude Code through it. That's the whole loop.
Start the gateway
just setup
just build
just runListens on :8443. Generates a CA and installs it into the system trust store the first time.
Route Claude Code through it
NODE_EXTRA_CA_CERTS=$HOME/.recondo/ca/ca.crt \
HTTPS_PROXY=http://localhost:8443 \
claudeEvery prompt, every tool call, every response — captured, hashed, persisted.
Inspect & verify
just recondo sessions
just recondo session sess_01HZ…
just recondo verify sess_01HZ…CLI inspector ships with the binary. Re-hash captures any time and compare.
Open source. Apache 2.0. Self-hosted.
Recondo is a Rust gateway, a TypeScript GraphQL API, and a React dashboard — all in one repository. Run it on your laptop with SQLite + local filesystem. Run it in your VPC with PostgreSQL, S3 Object Lock, and a customer-managed KMS key. Either way, agent traffic never leaves your environment.